IVO Networks
Technical Blog
Insights on enterprise networking, VPN infrastructure, security best practices, and cloud connectivity.
IPv6 Translation
NAT-APP46: Building a Real-Time Stateless IPv4-to-IPv6 Protocol Engine
A technical walkthrough of how APP46 performs real-time stateless IPv4-to-IPv6 translation at the client, covering RFC 7915/6052 compliance, address mapping, TCP session handling, and the engineering decisions behind a protocol engine that runs transparently as a Windows service.
Read more →
Hardware
GPU-Accelerated Network Appliances: CUDA Kernel Offloads on NVIDIA Coprocessors
How IVO Networks leverages NVIDIA CUDA coprocessors to offload computationally intensive packet processing — including encryption, deep packet inspection, and traffic classification — from general-purpose CPUs to dedicated GPU cores for dramatic throughput gains.
Read more →

Hardware
High-Performance Network Modules Architecture: Partnering with NVIDIA for ConnectX-6, RSS, and Multi-Queue Packet Distribution
An inside look at how IVO Networks appliances use NVIDIA ConnectX-6 (Mellanox) powered network modules with Receive Side Scaling and multi-queue packet distribution to achieve wire-speed processing across multiple CPU cores — eliminating bottlenecks in high-throughput VPN and security workloads.
Read more →
Engineering
Engineering a Linux-Based Appliance OS for Network Security Hardware
The process of building a minimal, security-hardened Linux distribution purpose-built for network appliance hardware — from kernel configuration and driver selection to read-only root filesystems, automated recovery, and secure boot chain validation.
Read more →
Engineering
IKEv2 VPN Architecture: Session Lifecycle, Rekeying, and Scale to 50,000+ Concurrent Tunnels
When enterprise customers ask how many concurrent VPN sessions a single appliance can sustain, the answer depends far less on raw throughput than on how the platform manages tunnel lifecycle at scale. At IVO, we engineered our IKEv2 implementation to handle 50,000+ concurrent tunnels — not by overprovisioning hardware, but by designing the session management […]
Read more →
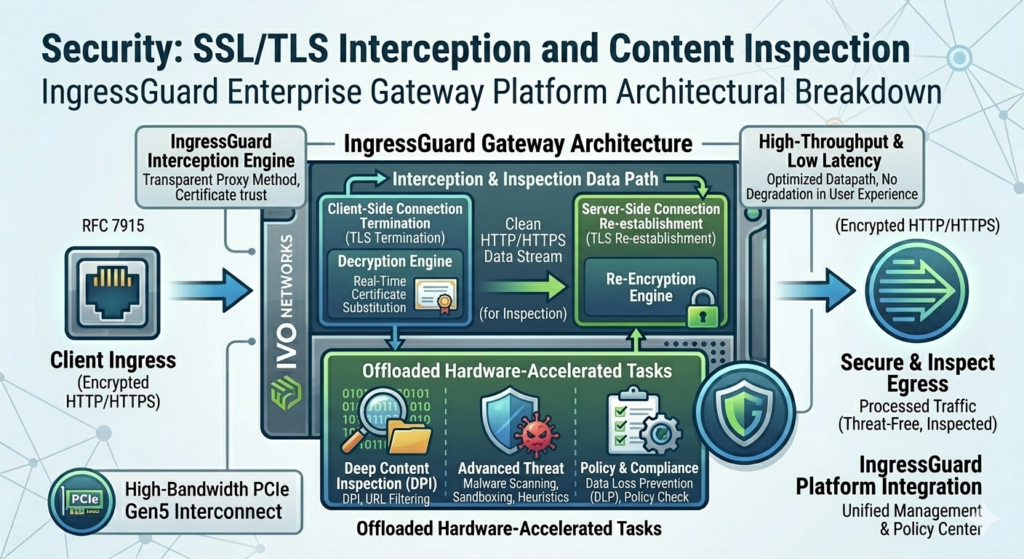
Security
SSL/TLS Interception and HTTP/HTTPS Content Inspection in Enterprise Security Platforms
Breaking down the architecture of SSL/TLS interception in gateway appliances — how IngressGuard performs real-time certificate substitution, content inspection, and threat detection on encrypted HTTP/HTTPS traffic without degrading user experience or throughput.
Read more →

Engineering
Granular Access Controls: Building a Policy Engine for Enterprise and Government Deployments
Access control in enterprise and government networks is not a binary gate. It is not simply “allow” or “deny.” The real requirement is far more nuanced: allow this user, on this device, from this network, to access this specific application — and restrict everything else. Building a policy engine that evaluates those conditions in real […]
Read more →
Engineering
Firewall Engineering: Rule Engines, Signature Matching, and False Positive Management
The hardest problem in firewall engineering is not detection. It is the space between detection and noise. A firewall that catches every SQL injection attempt but generates hundreds of false positives per day is a firewall that gets its alerts ignored. A firewall that never fires a false positive but misses real attacks has a […]
Read more →

Compliance
FedRAMP Authorization While Maintaining Continuous Delivery
The practical reality of pursuing FedRAMP authorization for network security products without freezing your release pipeline — how to structure continuous monitoring, automate OSCAL documentation, maintain an Authority to Operate, and still ship updates on a regular cadence.
Read more →

Zero Trust
Zero-Trust Remote Access: Architecting Secure Connectivity for Enterprise and Government
Designing a zero-trust remote access architecture that satisfies both enterprise security teams and government compliance requirements — combining always-on VPN, conditional access, TPM attestation, endpoint health verification, and continuous authorization.
Read more →
Zero Trust
Multi-Protocol Authentication in Zero-Trust Platforms: Kerberos, RADIUS, and Policy-Based Access
Implementing Kerberos ticket-based authentication alongside RADIUS for network access control in a zero-trust architecture — how IVO Networks appliances enforce policy-based access decisions using identity, device health, and conditional access rules.
Read more →

Networking
DNS Resolution at Scale: DNS64, NAT64, and NRPT in Enterprise Deployments
How DNS64 and NAT64 work together to enable IPv6-only clients to reach IPv4 servers, the role of Name Resolution Policy Tables in directing DNS queries across split-tunnel VPN environments, and common pitfalls that break enterprise DNS resolution at scale.
Read more →
Have a networking challenge?
Our team can help you design the right solution for your environment.
Contact Sales